Building Safe FinTech Systems in AWS, Azure, and GCP
(FinTech Series — Part 2)
This is the second article in my FinTech Series, where I break down how to build financial technology systems that are secure, reliable, and ready for real-world use.
Today, we’re talking about something important:
How do we build FinTech platforms safely using AWS, Azure, and Google Cloud?
Not just “how to deploy servers.”
But how to build systems that handle money, customer data, and transactions — without breaking, leaking data, or causing chaos.
Let’s make this simple.
What Makes FinTech Different?
FinTech systems are not normal apps.
They deal with:
People’s money
Personal information
Legal regulations
Security threats
High customer expectations
If a social media app goes down, it’s annoying.
If a payment system goes down, people panic.
So we must build differently.
Step 1: Think About Risk First
Before writing code, we ask:
What data are we storing?
Is it private?
How fast must we recover if something breaks?
Who is allowed to access it?
What happens if a server fails?
In FinTech, we don’t start with convenience.
We start with safety.
Step 2: Why Use AWS, Azure, and GCP?
All three cloud platforms give us powerful tools.
But they each have strengths:
AWS is strong in identity and database services.
Azure works very well with enterprise identity systems.
GCP has powerful networking and analytics tools.
A strong FinTech system can work in any of them — as long as we design it correctly.
The cloud is just the toolbox.
The design is what matters.
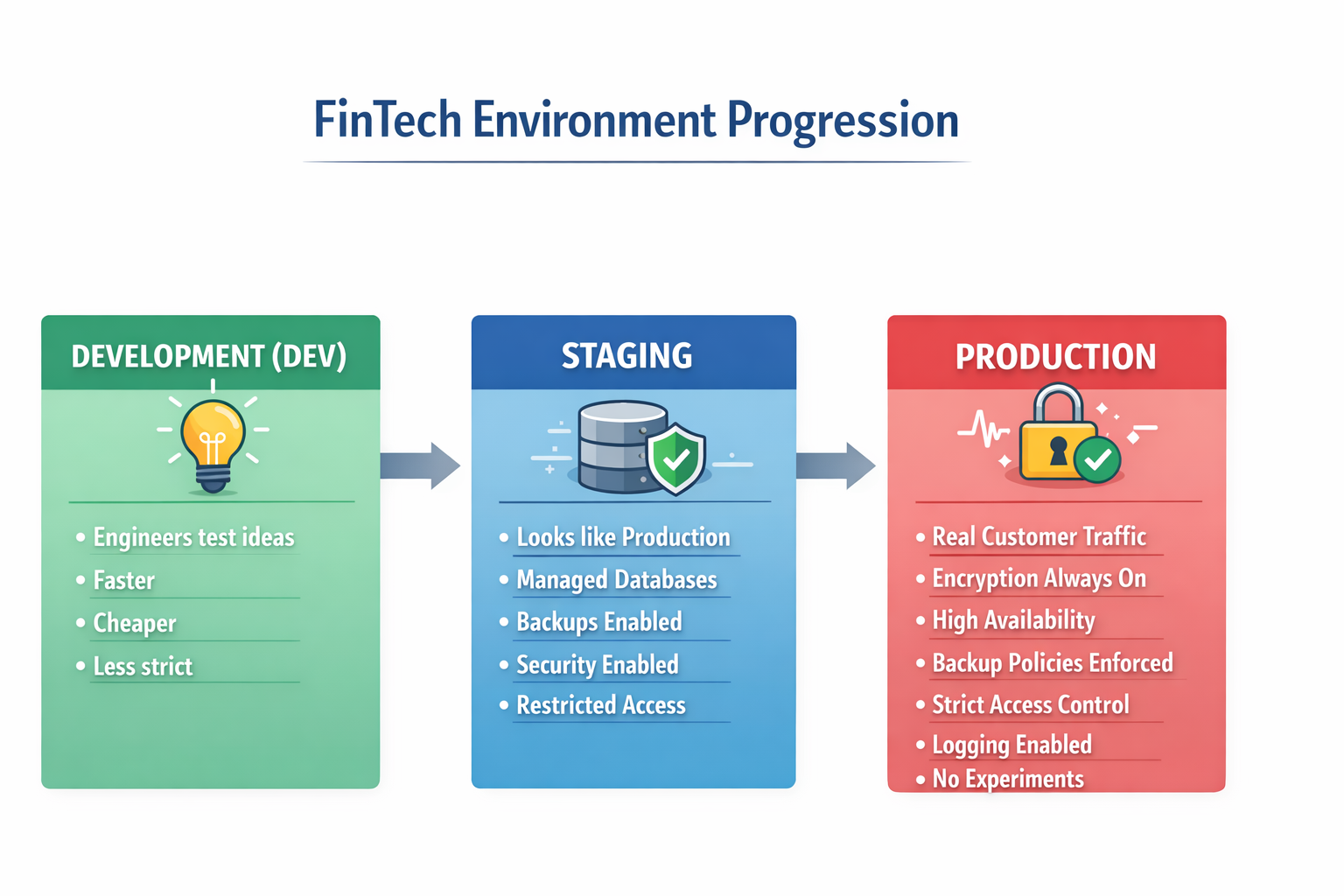
Step 3: Separate Environments (Very Important)
We never treat all environments the same.
We use three main environments:
Development (Dev)
This is where engineers test ideas.
Faster
Cheaper
Less strict
Staging
This looks like production.
Managed databases
Backups turned on
Security enabled
Restricted access
Production
This is real customer traffic.
Encryption always on
High availability
Backup policies enforced
Strict access control
Logging enabled
No experiments
Production is sacred in FinTech.
Step 4: Use Infrastructure as Code (With Rules)
We use tools like Terraform to define infrastructure in code. But in FinTech, Terraform is not just automation.
It becomes a safety system.
We:
Validate before deploying
Review changes before applying
Never apply directly to production
Track everything in Git
Detect configuration drift
This makes changes predictable and traceable.
Step 5: Protect Secrets and Data
Never store passwords in code.
Across AWS, Azure, and GCP, we use secure secret managers.
We also:
Encrypt data at rest
Use TLS encryption in transit
Follow least privilege access
Rotate secrets regularly
Security is not optional in FinTech.
It is the foundation.
Step 6: Be Ready for Incidents
Things break.
Servers fail. Networks glitch. Databases slow down.
In FinTech, we need structure:
Clear severity levels
Defined escalation path
Communication updates
Evidence capture
Root cause analysis
Postmortem documentation
We don’t guess during outages.
We follow procedure.
Step 7: Disaster Recovery (Plan for the Worst)
We define two important things:
RTO — How fast must we recover?
RPO — How much data can we afford to lose?
Then we design the system around those answers.
We use:
Multi-zone databases
Automated backups
Cross-region replication
Restore testing
Backups don’t matter if you’ve never tested restoring them.
Step 8: Watch for Drift
Sometimes infrastructure changes without being planned.
That’s called drift.
In FinTech, drift equals risk.
So we:
Monitor configuration
Generate drift reports
Store evidence
Review changes regularly
Trust comes from visibility.
Step 9: Kubernetes in FinTech
If we run containerized apps:
Limit admin access
Isolate namespaces
Control secrets
Use managed databases
Enable audit logs
Kubernetes is powerful — but must be controlled carefully.
The Real Goal
Building FinTech systems in AWS, Azure, and GCP is not about being “multi-cloud.”
It’s about:
Security
Reliability
Governance
Risk control
Operational maturity
If your system can survive:
An audit
A regional outage
A security scan
A Sev-1 incident
Then you are building correctly.
This Platform Is Evolving
The FinRegOps Multi-Cloud platform is the original foundation.
It will continue evolving to include:
Policy-as-code
Automated compliance validation
Advanced network isolation
Secret synchronization
Security posture scanning
This is version one of something much bigger.
Want Access to the GitHub Repo?
We are opening access to the evolving repository. Join the list and get access to the GitHub repo.
Once you join the list, we’ll send access details.
In the next article in the FinTech Series, I’ll break down: How to design identity and access controls properly in financial systems.
If you’re building in AWS, Azure, or GCP, and especially if you’re working in financial services, this series is for you.
Stay tuned.